Decentralized Storage: Exploring IPFS and Swarm for Secure and Scalable Data Management
In today’s blog, we dive into the fascinating world of decentralized storage, a game-changer in the blockchain industry. With the increasing abundance of data and concerns over centralized control, decentralized storage offers a revolutionary solution. We’ll explore the concept, compare it to centralized storage, and delve into two popular decentralized storage systems: IPFS and Swarm.
Decentralized Storage: An Overview
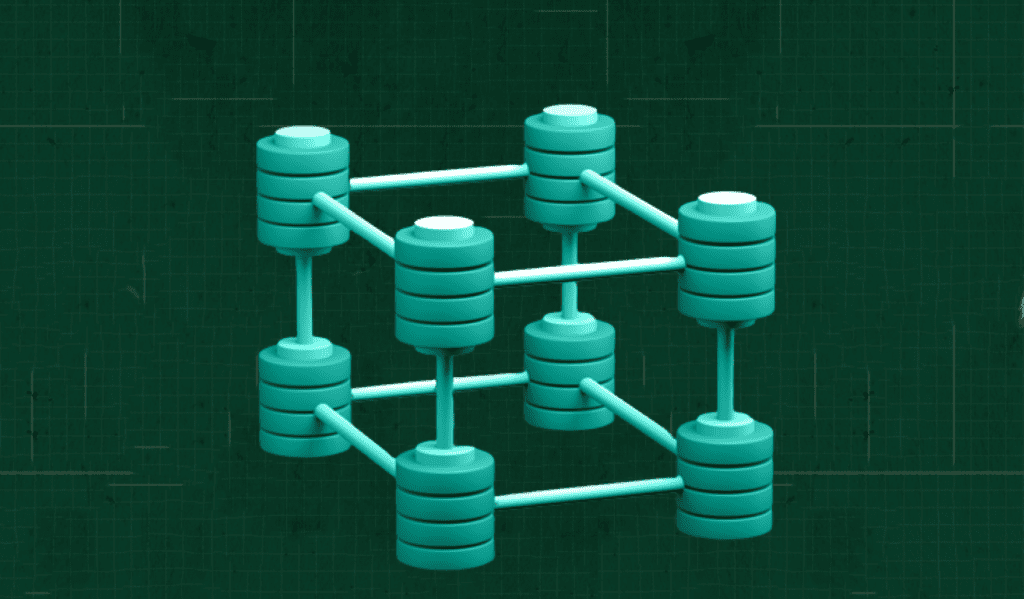
Traditional centralized storage involves data being controlled by a single entity, posing risks of privacy breaches and single points of failure. Decentralized storage, on the other hand, leverages a network of distributed storage nodes across a geographic area. For the outside world, this system appears to be a single entity, but the data is spread across all the nodes. The main benefit of this system is that no one owns the network. This approach eliminates a centralized authority, ensuring data security and accessibility.
Advantages over Centralized Storage:
1. Reducing Risks: Decentralized storage mitigates risks associated with leaking private information and single source failures.
2. Consistent Data: Unlike centralized storage, decentralized systems ensure consistent data across all nodes.
3. Scalability: Decentralized storage systems, such as Ethereum and IPFS, offer scalability by offloading data to multiple nodes.
4. Easy Access: Clients can access the nearest storage node, enhancing accessibility and reducing latency.
InterPlanetary File System (IPFS):
IPFS is one of the most popular decentralized storage systems available in the market today. IPFS uses decentralized storage mechanisms along with content hashing methods to store data in order to avoid duplication and consistency of data. So, what is content hashing?
In our current internet, we have tons of redundant data. So, we have the same cat image lying around as different copies as their URL is different. Another example is if we upload a user profile picture to different social media websites, every social media account will have a copy stored in their database, even though all they are the same.
But the IPFS network uses CONTENT BASED HASHing. Which means when a picture is uploaded into the network, then the image is hashed and then is represented using a hash digest value. So, even though we upload the same image multiple times, by the principles of cryptography, the same hash should be generated. By using the hash digest, the system can prevent uploading multiple copies into the network and will return the hash generated earlier. And we also know that the hashing function will yield a different result even for a small pixel change in the picture used. Thus, we can also verify the genuinity of the asset.
How does IPFS store data ?
The IPFS network stores data in an Object format. The IPFS object consists of two attributes. They are Data and Links.
Data : The data part actually stores the actual data that the user is trying to save. The maximum amount of data that can be stored in it is 256kb. The data can be of any format.
Links: The Links attribute contains the reference to the next object that contains the remaining data.
Let us assume that we are saving an image of size 456 kb. For that, the image is first broken into data chunks of size not more than 256 kb. And the chunks are converted into IPFS objects. The IPFS object with the first 256kb contains the link to the next object and thus so far. The last object contains NULL to represent the end of the data.
What is SWARM?
Swarm is a peer-to-peer network designed to provide decentralized storage and communication infrastructure. The nodes in the network are called Bee Nodes or Bees that collectively offer resistance to data censorship and function as a permissionless storage system.
It is a permissionless data storage system that is designed to provide scaling base layer storage infrastructure for the internet to decentralize. Its incentive system is enforced through smart contracts on the Gnosis Chain blockchain and powered by the xBZZ token, making it economically self-sustaining.
The swarm network can be divided into 4 major parts
- Underlay network : The base protocol layer of the system to provide transport of data.
- Overlay network : The network layer to provide support for distributed immutable storage of data chunks.
- Data Access Layer – A component providing high-level data access and defining APIs for base-layer features.
- Application Layer – An application layer defining standards and outlining best practices for more elaborate use cases.
The swarm network incentivizes the users in two different ways. One is for the users that have shared their storage space for the network. And second is for the users that are sharing their bandwidth, ensuring the network’s self-sustainability.
The Importance of Decentralized Storage:
Decentralized storage democratizes data control, mitigates risks, and fosters innovation. By empowering users with ownership and control over their data, decentralized storage paves the way for a more secure and accessible digital landscape.
Conclusion
Decentralized storage, such as IPFS and Swarm, revolutionizes the way we handle data in the blockchain industry. By addressing the limitations of centralized storage, these systems enhance data security, accessibility, and scalability. As the demand for reliable and decentralized solutions grows, the role of decentralized storage will continue to shape the future of data management.
Embrace the power of decentralized storage and unlock a new era of data security and accessibility.

is an experienced blockchain engineer with keen understanding of EVM based blockchain networks, smart contracts and web3 protocols. He has a successful track record of working with various DeFi protocols, NFT projects and web3 projects. He is currently working as a Blockchain Engineer at Nonceblox Pvt Ltd and shows a vivid interest in tech talks and loves to explore various technologies like networking, web3, cryptography.